ViPNet CSP
2.9

Download
Category: Data protection
System: Windows XP, Vista, 7, 8.1, 10
Program Status: Free
Looking at the file: 43 556
Description
ViPNet CSP is a program that protects information using "cryptographic code". This software protects data according to certificates of the Federal Security Service of Russia, as well as according to current GOSTs. ViPNet CSP provides protection in a "keyed digital form" (signature). This digital signature protects information in enterprises that use electronic document processing. This client works according to crypto provider standards in different organizations and firms.
Features
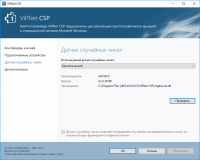
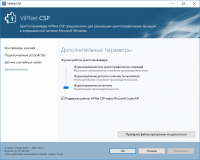
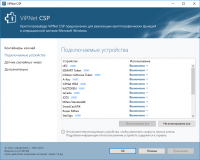
The main feature of ViPNet CSP is the recording of "digital keys" and access (token) on an external device. All new devices are connected via the "PKCS#11" interface. You import and export "keys" in #PKCS12 format. In this program you can not only add and verify electronic signatures, but also compare hash, encryption and imitoprotection of information according to all parameters of GOST. Using encryption and imitization, you can prepare the delivery of reports electronically. This program is not easy to learn, so you will have to spend a lot of time to study its interface and capabilities. The cryptographic protection of this program is integrated with Microsoft CNG and CryptoAPI applications. This client works over secure channels, transmitting data to different sites.Versions
If necessary, you can download ViPNet CSP in the standard version with a basic set of functions and tools for operation. It works with "class" KS1 protection. If you need protection at a professional level, then use a paid software that protects documents in the "KS" and KS3 classes. Regardless of which version of the program is installed, each user receives protection in cryptographic format, as well as documents with detailed instructions for full-fledged work. The best analog of this program is CSP Cryptopro, which contains many features, but is not designed for the beginner and is difficult to operate.Key features
- the program is available for download in three versions with different protection class;
- all elements of cryptographic protection comply with GOSTs and regulations;
- the program can be integrated with software such as Microsoft CryptoAPI;
- the program can protect electronic documents by adding special signatures and certificates;
- the software can be operated on a flash drive or an external hard disk as tokens.
Download ViPNet CSP
See also:
Comments (0)